CimTrak for Workstations
Secure Your Workstations from IT Security Threats
Monitoring workstations and desktops can be necessary for a number of reasons, including mitigating security risks and compliance with PCI-DSS, CMMC, and many others. As part of the comprehensive CimTrak product line, CimTrak for Workstations/Desktops ensures the integrity, security, and compliance of these machines on a continuous basis.
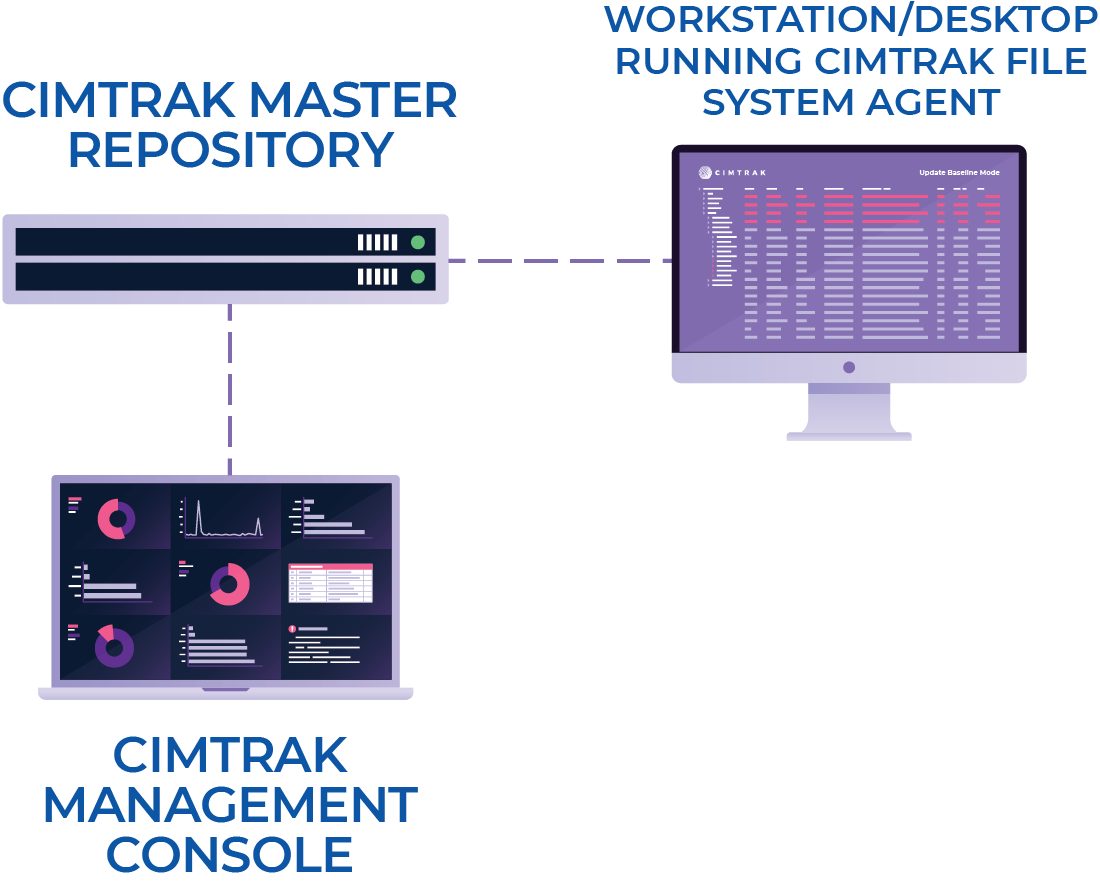
How CimTrak for Workstations/Desktops Works
In the same way CimTrak monitors other critical infrastructure such as servers, network devices, cloud configuration, and databases, CimTrak for Workstations/Desktops detects and alerts to changes that are unknown, unexpected, and unauthorized.
Using CimTrak's real-time capability, you can quickly detect security threats and mitigate them with the power to roll back and remediate—preventing or restoring unexpected changes before they cause problems.
By giving you one easy-to-use tool that covers all systems within the IT environment, CimTrak greatly simplifies the process of detecting security threats and breaches while also providing continuous compliance with regulations such as HIPAA, NERC-CIP, FISMA, and PCI-DSS.
Get Complete Change Details
CimTrak gives you deep forensic insight into changes that are occurring on your workstaions. By letting you know “who” made a change, “what” exactly changed, and “when” it changed, users get actionable information, not just an alert that requires time-consuming, manual effort to investigate. Users can drill down further and get a side-by-side comparison of what a particular file, configuration, schema, etc. looked like pre-change vs. post-change and zero in on exactly what changed. This extraordinary level of detail saves already stretched IT staff time, money, and frustration by getting to the root of the problem.
Extensive Alerting and Reporting Capabilities
With a wide selection of reports that can be scheduled or created on-demand, CimTrak ensures you have the information you need for auditing, compliance, configuration, and change management purposes. With CimTrak’s ODBC driver, data can be sent from the CimTrak Master Repository to any reporting tool your organization utilizes including Excel, Crystal Reports, or Cognos.
Upon detection of changes, alerts can be sent to the appropriate personnel within your organization. Additionally, change details can be sent to a Syslog server or security information and event manager (SIEM) to assist in the prioritization or risk analysis and threat detection. CimTrak also offers out-of-the-box integration with all major SIEM solutions, including HP ArcSight, LogRhythm, IBM QRadar, McAfee Enterprise Security Manager, RSA Security Analytics, Splunk, and more!
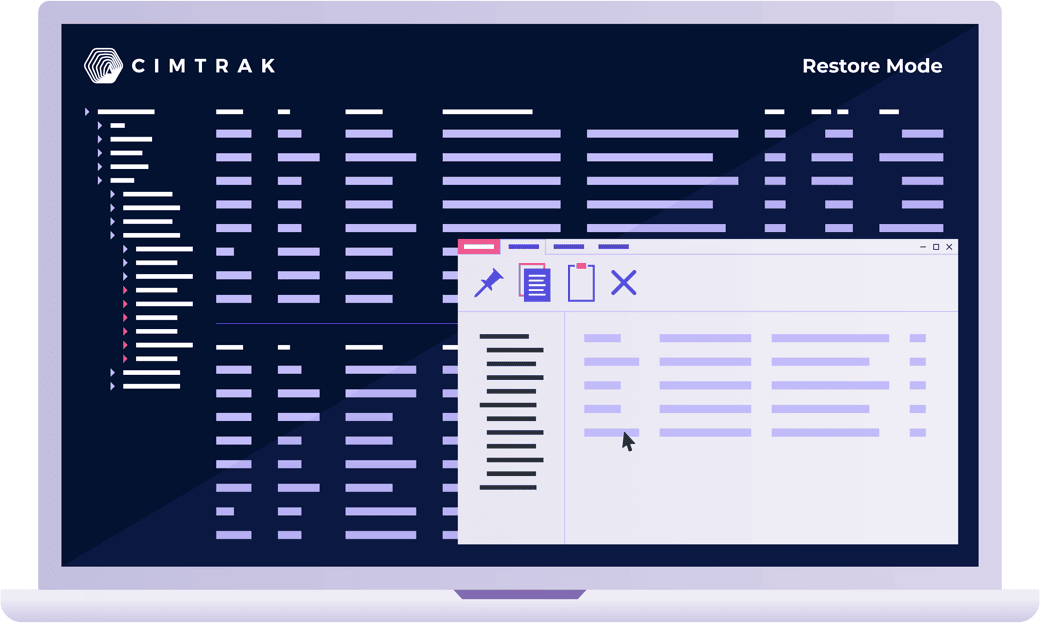
Restore File Changes or Prevent Them Completely
CimTrak’s unique architecture gives it the unprecedented ability to go beyond simply change detection. Various modes of operation including “update baseline,” deny rights,” and “restore” give users extreme versatility, unlike any other solution in the market.
Users can deploy these modes of operation selectively to monitor a particular file or group of files as appropriate. This granular nature of deployment allows precision monitoring of your unique environment in a way that fits your operational needs.
Log
Changes are logged and alerted and a detailed audit trail is created.
Update Baseline
An incremental “snapshot” of a file, configuration, or setting is taken and stored in the CimTrak Master Repository as changes occur. This feature allows for changes between snapshots to be analyzed and the previous baseline to be redeployed at any time with one click.
Restore
Instantaneously reverses a change upon detection. This effectively allows a system to “self-heal.”
Deny Rights
Denies any access to modify a file. Since CimTrak runs as the local system account, it does not matter what privilege access a user has. The ability to manipulate a file will not be allowed, thus denying changes, deletions, or additions.
Proactively Respond to IT Security Threats
When changes occur, CimTrak’s unique ability to take proactive action via the “deny right” or “restore” mode, helps to ensure the integrity and security of your business-critical servers, workstations, and devices. CimTrak protects against external attacks that slip by your perimeter defenses as well as internal attacks and occasional accidents that originate from inside your corporate perimeter.
While intrusion detection systems and anti-virus are essential, they are dependent on known attack signatures and they are often useless against zero-day attacks, disgruntled employees, or programmer mistakes. CimTrak is not dependent on outside intelligence of new hacker or virus methods.
As cyber-attacks, data breaches, and new forms of malware become more and more prevalent, new methods of defense are necessary. With CimTrak’s powerful and unique modes of operation, you can detect, respond, and recover from changes resulting from both malicious or circumvented activities. This ensures your environment is compliant and remains secure as new and evolving IT security threats try to wreak havoc on your IT systems.


