If you've ever felt that keeping up with all the changes in cybersecurity is nearly impossible, you're not alone. As attack vectors evolve rapidly, today's IT security professionals need a repeatable, reliable framework for monitoring and managing their organization's environments.
Change monitoring is essential for managing risks, but it's not the only piece of the puzzle. Control and total management are critical, requiring a combination of innovative technologies and an effective security policy. In this article, you'll learn about the concepts of change control and change management, with a particular focus on how they matter to security administrators.
What is Change Control?
Change control is the end-to-end management of changes across your servers and network devices across the enterprise.
Typically, change control encompasses two related but separate concepts: change management and change monitoring. If you can't monitor changes, you can't manage them. To control your environment, you need the ability to analyze and respond to changes. The control process is best guided by a comprehensive, updated information security policy.
What is Change Monitoring?
Change monitoring is the ability to detect changes. In practice, this is accomplished with technologies such as File Integrity Monitoring Software (FIM).
Change monitoring should be automated to the greatest extent possible for convenience and accuracy. Certain activities, such as alert review, cannot be automated. However, using tools with built-in intelligence can significantly ease the time commitment required to monitor changes effectively.
Effectively administered change monitoring will encompass each of the following aspects:
- Centralized Audits: A single repository of changes made to critical files and configurations, which attributes changes by user, location, and time.
- Real-Time Change Reporting: The average cybercriminal completes data retrieval in just minutes. If your FIM tool completes weekly scans instead of real-time change detection, you could miss negative changes until long after the event has happened.
- Human-Readable Reporting: Alerts and reports that are easy for your administrative users to understand aren't strictly necessary, but they can significantly reduce error margins. Clear information can also reduce your time to respond.
- Intelligent Classification of Changes: A FIM tool smart enough to classify changes as positive, neutral, or negative allows administrators to focus on response.
- Unalterable Logs: To effectively monitor insider information security threats, unalterable data is critical to creating accountability.
Each of these elements for effective change monitoring may not be strictly necessary depending on your goals and risk tolerance. PCI guideline 11.5.2 requires organizations to perform critical file comparisons at least once weekly and automate the receipt of notifications. However, intelligent, real-time change monitoring supports effective change management and maximum risk mitigation.
What is Change Management?
Change management is the process of making decisions about your network, which is informed by a combination of effective security policy and change monitoring.
Security pros with a background in healthcare are familiar with the "three R's" necessary for effective patient outcomes: the Right Person, the Right Time, & Right Place. In the realm of security change management, the three Rs can be modified to include:
- Right Person: Administrative Access Governance
- Right Time: In Security, the Right Time is Real-Time
- Right Information: Without adequate documentation, including a comprehensive internal security policy and human-readable intelligence from your FIM solution, it's impossible to make the right decisions to protect your organization.
In practice, change management can encompass each of the following elements:
- Appropriate Access: Grant the minimum necessary permissions to establish accountability for administrative users and the ability to quickly and efficiently resolve end-user access issues.
- Policy-Based Guidance: In an ideal environment, policy and technology should work in tandem. For example, your password policy should guide the use of technology to automate required password changes and formats.
- Change Analysis: Changes to critical system files are frequent and necessary in most company networks. You need to be able to quickly and effectively differentiate between beneficial and risky changes.
- Accountability Workflows: Every user, including administrative users, should not have unchecked powers that are not logged.
- Task Automation: When you notice a negative change to a file, what's next? Can you quickly remediate the change directly from your centralized management portal, or are you forced to spend hours reconciling issues?
- Appropriate Documentation: Your policy and tools should support transparency by documenting the nature of the change, who made the change, and why the change was made. Ideally, your documentation should also reference any necessary approval obtained.
What's Necessary for Effective Change Management?
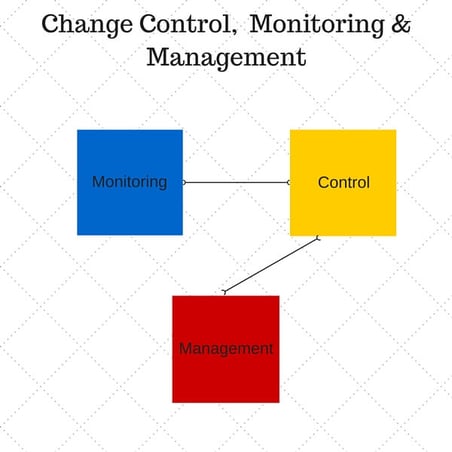
Ultimately, change monitoring, control, and management are closely related concepts. Your organization needs smart tools to effectively monitor for changes. These tools can also inform change control. A combination of policy and automation-based insight should be used to manage changes enterprise-wide.
CimTrak offers a smart baseline for a state-of-the-art approach to real-time change monitoring, centralized change control, and total change management. With built-in intelligence, your analysts can be informed of the quality of changes and perform total remediation directly from the management portal. To learn more, click here!
Tags:
Cybersecurity
April 29, 2025
.png?width=622&height=198&name=Change%20Monitoring%20(5).png)