In cybersecurity, technical solutions receive most of the attention. Organizations understandably want to know which firewall, EDR, or WAF they need to buy to keep their users, assets, and data safe from cyber-attacks.
And while technical security solutions are undeniably important, they aren’t the whole story. Organizations that need to protect against even moderately sophisticated attacks — which is most organizations — must go beyond technical controls to consider the people and processes involved in cybersecurity.
That’s where the CIS Organizational Controls come in.
What Are the CIS Organizational Controls?
The CIS Controls are broken down into three tiers:
-
Six Basic Controls
-
Ten Foundational Controls
-
Four Organizational Controls
Once the Basic and Foundational Controls are implemented, organizations will have a solid set of technical security controls in place. Even without implementing the final four controls, this will be enough to protect against the vast majority of cyber-attacks.
However, with the volume and sophistication of attacks rising all the time, a typical organization should expect to be targeted by more sophisticated attacks. When these attacks happen, it’s essential that you have the final tier of CIS Controls in place.
Unlike the Basic and Foundational Controls, the CIS Organizational Controls focus less on technical solutions and more on the people and processes needed to ensure ongoing security.
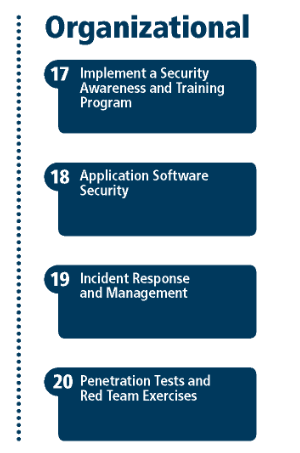
Image Source: cisecurity.org
Overview of the 4 CIS Organizational Controls
17. Implement a Security Awareness and Training Program
“For all functional roles in the organization (prioritizing those mission-critical to the business and its security), identify the specific knowledge, skills, and abilities needed to support defense of the enterprise; develop and execute an integrated plan to assess, identify gaps, and remediate through policy, organizational planning, training, and awareness programs.”
WHY IS THIS IMPORTANT?
Cybersecurity isn’t something to be done to an organization — it’s something to be done by an organization. Expecting the cybersecurity function to sit apart from other operational functions and "take care of security" is asking for trouble.
This CIS Organizational Control urges organizations to ensure that all operational staff receives a degree of security training appropriate to their role. For example:
-
Developers should be taught how to write code securely, and why it is important.
-
End users should be taught to identify common social engineering attacks, and how to report them.
-
Executives should be taught why cybersecurity is critical to the business, and how they can expect to see it deliver ROI.
HOW TO IMPLEMENT
The most important step here is to identify the security skills and knowledge needed by each operational function and perform a gap analysis. This should be used to design and deliver an initial program of security awareness training. Beyond this, there should be a standard process to ensure new hires are educated in their security responsibilities, and all staff receives regular top-up training. Many organizations choose to implement customized benchmarks.
18. Application Software Security
“Manage the security life cycle of all in-house developed and acquired software in order to prevent, detect, and correct security weaknesses.”
WHY IS THIS IMPORTANT
Application vulnerabilities are an easy way for a threat actor to gain access to a target network and/or steal sensitive information. Vulnerabilities are constantly being found in commercial software packages, and threat actors are quick to ‘weaponize’ them into exploit kits. Internally-developed applications are also prone to vulnerabilities, which are typically introduced as a result of coding or logic errors, incomplete requirements, and a lack of rigorous testing.
Vulnerabilities in applications — particularly those that are Internet-facing — pose a huge risk. Having a formal, well-executed process to prevent, identify, and remediate vulnerabilities is essential.
HOW TO IMPLEMENT
For commercially bought software, organizations don’t have control over the introduction of vulnerabilities during development. Protecting these assets requires a process for vetting applications and vendors prior to purchase, and an ongoing process to identify and patch known vulnerabilities. This aspect of security is also covered by CIS Control #3: Continuous Vulnerability Management.
The process required to ensure the security of internally-developed applications is known as the Secure Development Lifecycle (SDLC). It incorporates everything from establishing secure coding practices to rigorous and regular security testing using a combination of manual and tool-assisted techniques.
Implementing an SDLC is not an overnight fix — it requires clear planning and oversight to implement and maintain. However, once in place, the SDLC process will significantly reduce the number of vulnerabilities introduced during development, and quickly identify them when they arise.
19. Incident Response and Management
“Protect the organization’s information, as well as its reputation, by developing and implementing an incident response infrastructure (e.g., plans, defined roles, training, communications, management oversight) for quickly discovering an attack and then effectively containing the damage, eradicating the attacker’s presence, and restoring the integrity of the network and systems.”
WHY IS THIS IMPORTANT
Cyber incidents are a fact of business, and even the most well-protected organizations can’t block every attack. When a threat actor or group is successful in gaining some level of access to an organization’s network or assets, there must be a strong set of processes in place to identify, manage, and recover from the incident — including the removal of all traces of the attacker’s presence.
If such processes are not in place at the time of an incident, there is a strong chance that the incident will be mismanaged. In the worst cases, attackers can have a foothold within a target network for months or years before their presence is identified.
HOW TO IMPLEMENT
This CIS Organizational Control is largely about developing processes and assigning duties. If everybody in the security function knows precisely what to do, how to do it, and where to report/record it, the incident response function will typically perform well.
Beyond this, there should be a way to test that processes and duties are effective before a cyber incident occurs. This is usually done by conducting regular incident response exercises and scenarios — sometimes called war games.
20. Penetration Tests and Red Team Exercises
“Test the overall strength of an organization’s defense (the technology, the processes, and the people) by simulating the objectives and actions of an attacker.”
WHY IS THIS IMPORTANT
Of all the CIS Controls, the final Organization Control is the most advanced.
While many organizations have good intentions for their cybersecurity processes and policies, ensuring their continued implementation is far from easy. For example, your organization might have a policy of implementing critical security patches within 48 hours of release, but logistically this may not always happen (or even be possible).
Penetration testing and red team exercises are used to identify weaknesses in security tools, policies, and practices under realistic but non-threatening conditions.
HOW TO IMPLEMENT
The obvious way to implement this control is simply to perform penetration tests and red team exercises. However, these processes are only valuable if they are completed regularly and in a way that genuinely tests the security capabilities of your organization. For example, many vendors offer penetration tests that are more compliance-focused than security-focused — for obvious reasons, these services are not appropriate for the purpose of this CIS Organizational Control.
Ideally, organizations should define and implement a program of penetration testing and red team exercises designed to push the limits of its cybersecurity capabilities.
Implement CIS Organizational Controls with CimTrak
CimTrak is an IT integrity, security, and compliance toolset that helps any organization implement and maintain the CIS Organizational Controls.
CimTrak continuously monitors your environment and detects changes to assets, files, and accounts. When specified changes occur, CimTrak raises an alert and a report, making it easy to identify security issues in hardware and software assets.
Critically, CimTrak provides full or partial coverage for 17 of the 20 CIS Controls, including three of the CIS Organizational Controls.
Using CimTrak your organization can:
-
Establish a process to accept and address software vulnerability reports, and communicate progress to your security group. For applications that rely on a database, CimTrak includes standard hardening configuration templates based on industry best practices. (CIS Control 18)
-
Quickly report IT anomalies and incidents to incident responders, and publish information to all members of your incident response workforce. (CIS Control 19)
-
Control and monitor accounts associated with penetration testing providing an audit trail of all changes helping to ensure systems are being used for legitimate purposes. (CIS Control 20)
To find out more about how CimTrak can help your organization align its security strategy and processes with CIS Controls, download the solution brief today.
Tags:
Compliance
July 30, 2020