Compliance
Continuously comply with major regulatory requirements

How CimTrak Helps
CimTrak's Compliance Module provides the necessary auditing, alerting, and reporting capabilities to maintain and demonstrate continuous compliance and assurance.

CimTrak aligns with CIS Controls.

CimTrak helps maintain PCI-DSS Compliance.

CimTrak helps with GDPR Compliance.

CimTrak helps with CMMC controls and requirements.
![]()
CimTrak aligns with CIS Benchmarks

CimTrak helps with SWIFT Customer Security Controls Framework.

CimTrak helps maintain HIPAA Compliance.
CimTrak supports Gramm-Leach Bliley Act (GLBA) requirements.
CimTrak helps with SOX Compliance.
CimTrak aligns with NIST 800-171 Compliance.

CimTrak helps with Federal Information & Security Management Act (FISMA) requirements.

CimTrak aligns with NERC-CIP regulations and requirements.
CimTrak helps with CJIS requirements.

CimTrak aligns with CMS and its Information Security & Privacy Acceptable Risk Safeguards (ARS).
CimTrak helps with Continuous Diagnostics and Mitigation (CDM).

CimTrak aligns with 1/4 of SOC2 reports and control requirements outlined by AICPA.

CimTrak helps with FedRAMP compliance by ensuring security and integrity across the infrastructure.

CimTrak helps with achieving compliance with APRA prudential standard CPS 234
50+ Supported Regulatory and Compliance Mandates
-
"CimTrak does what it says it does—without a lot of heaviness and problems. It gives us assurance against things we cannot see or things that are hard to identify, like malware. All forensic post-event investigation and damage is prevented by the use of CimTrak."
John Keese, Head of Compliance, Zoom
-
"We use CimTrak for PCI compliance, and it does everything it should. We are constantly monitoring for changes to our sites, and it does exactly what we need it to do. The product is simple to use and pretty hands-off.
Mike D., American Specialty
-
"Cimcor makes compliance pleasant and enables us to be much more in control than we've had in the past... My lead engineers speak very highly of Cimcor's engineers and CimTrak has saved us thousands of dollars while delivering ROI."
Justin Quevedo, Power Supervisor, Tacoma Power
TRUSTED BY




_200px.png.png?width=80&height=68&name=U_S_Air_Force_(USAF)_200px.png.png)
Continuously gather evidence and documentation for your audits
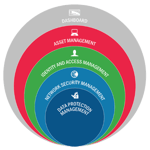
Major regulations including SOX, PCI, HIPAA, FFIEC, FISMA, NERC-CIP, SWIFT, GDPR, CDM, and CJS require organizations to think critically about their IT infrastructure and how it impacts compliance.
CimTrak helps you establish and maintain compliance with these regulatory benchmarks while simultaneously improving the overall security and audit-readiness of your IT infrastructure.


Understand your security posture throughout your infrastructure
Leverage CIS Benchmarks and DISA STIGs to validate if your systems are configured and in a hardened state.
Based on hardening assessments, CimTrak can provide detailed reports and remediation guidance.
Flip Boxes
Learn How to Use Sprocket Rocket
Sprocket Rocket lets you transform your rapid prototype into a beautiful
design by adjusting every aspect of the design to fit brand standards.
Flip Box Front
(Left Flip)
Flip Box Front
Add icons, images, buttons, and other things.
Flip Box Front
(Right Flip)
Flip Box Front
Add icons, images, buttons, and other things.
Flip Box Front
(Top Flip)
Flip Box Front
Add icons, images, buttons, and other things.
Flip Box Front
(Bottom Flip)
Flip Box Front
Add icons, images, buttons, and other things.
Transparent BG
Transparent BG
Add icons, images, buttons, and other things.
Solid BG
Solid BG
Add icons, images, buttons, and other things.
Gradient BG
Gradient BG
Add icons, images, buttons, and other things.
Image BG
Image BG
Add icons, images, buttons, and other things.
Flip Box Front
(Left Flip)
Flip Box Front
Add icons, images, buttons, and other things.
Flip Box Front
(Right Flip)
Flip Box Front
Add icons, images, buttons, and other things.
Flip Box Front
(Top Flip)
Flip Box Front
Add icons, images, buttons, and other things.
Flip Box Front
(Bottom Flip)
Flip Box Front
Add icons, images, buttons, and other things.
Compliance Features
Compliance
made simple

CONSOLIDATED DASHBOARD
One login for all of your File Integrity Monitoring and compliance needs. The CimTrak Compliance Module is fully integrated with our core product to simplify and correlate security and integrity management activities into a single pane of glass.
COMPLIANCE MAPPINGS
Create a custom set of benchmark tests to get custom-fit compliance. Compliance mappings enable you to comply with your specific standards by tailoring them to exactly what you need.
BENCHMARK SCANNING
Upload compliance benchmarks to the Compliance Module for testing, auditing, reporting, and managing remediation to stay consistent with hardening standards.
NETWORK DISCOVERY
Collect information about physical assets and assign them to a compliance policy with one click. Network Device Discovery helps you keep tabs on your routers, switches, servers, hosts, and firewalls.
EASILY CREATE POLICIES
Track changes and deviations from your compliance policy by regularly scanning your devices. Policy and mapping creation is simple and can be customized.
REPORTING
Easily access reports on your current and historical compliance according to industry standards and compliance requirements. Ensure you're always audit-ready.
WAIVER MANAGEMENT
Exceptions happen. Every IT infrastructure is different. Easily allow policy conditions and make those exceptions. These exceptions will be highlighted as a waiver for future auditing activities.
AGENT & AGENTLESS
Assess your security posture using CIS benchmarks or DISA STIGs using our agent-based solution or remotely via our agentless technology.
CimTrak Product PDF
Get the CimTrak Technical Summary
Get a copy of our CimTrak Technical Summary, our in-depth guide to all its capabilities.
Try CimTrak for Free
Get your Free 14-day trial of CimTrak
Just let us know what capabilities you want to test out, and we'll set up a trial in your environment.


