BMC and CimTrak
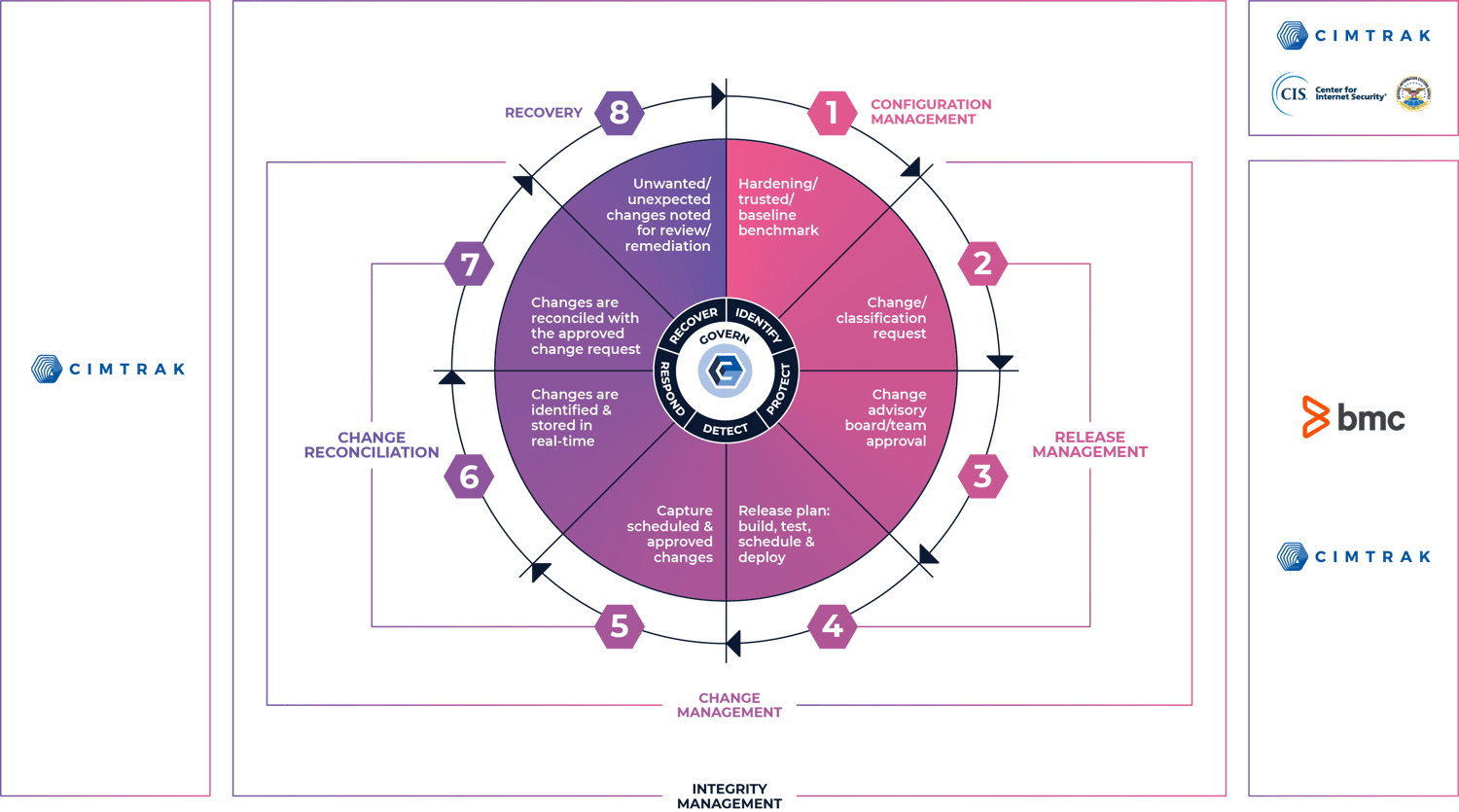
Closed-Loop Change Control Process
Mitigate Security Threats and Breaches
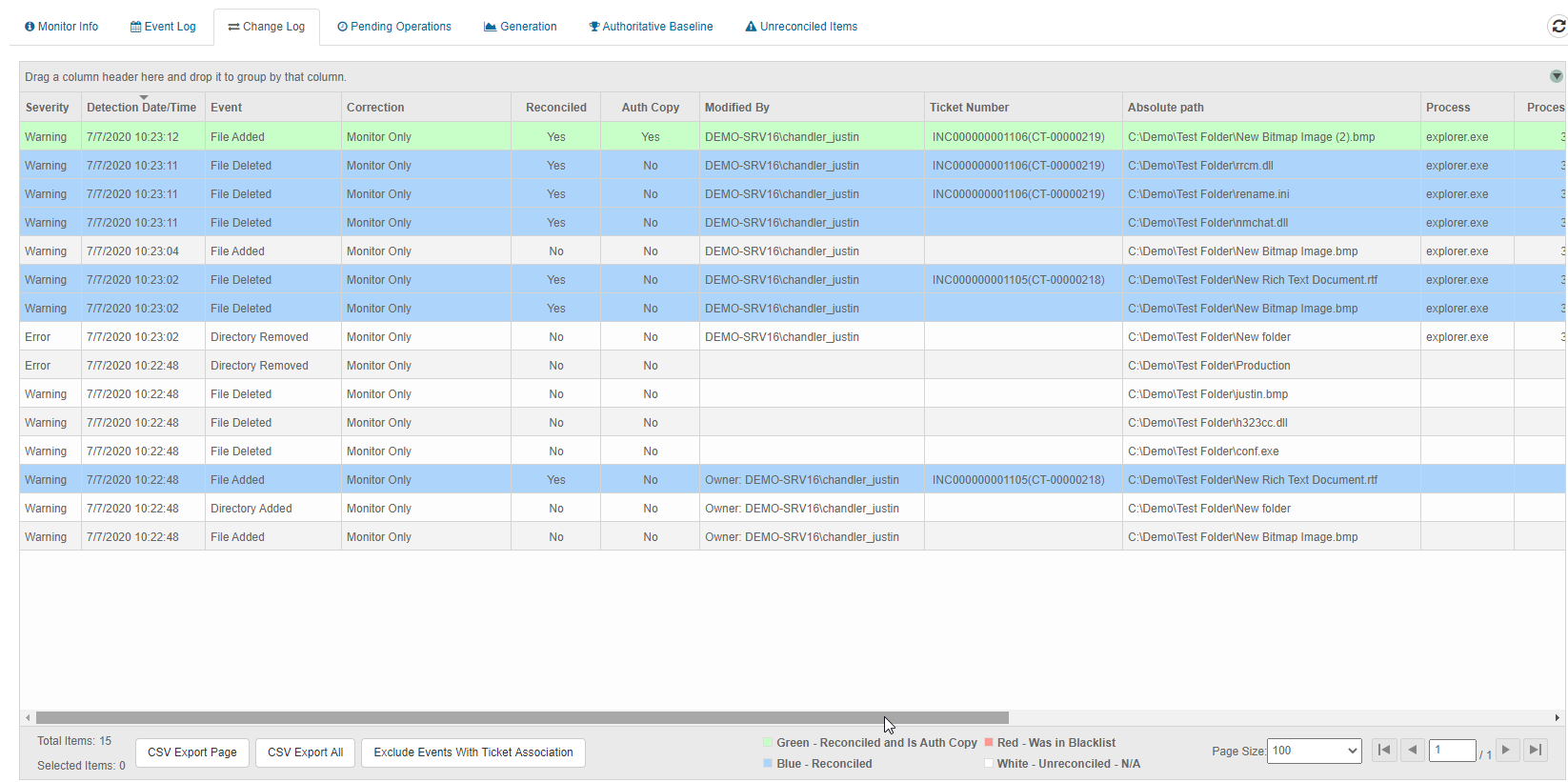
The CimTrak Integrity Suite monitors and protects a wide range of physical, network, cloud, and virtual IT assets in real-time while providing detailed forensic information about all changes. CimTrak allows organizations to proactively safeguard their critical data and systems through unauthorized change detection and automatic remediation, ensuring compliance and security are maintained at all times.
BMC and Cimcor have teamed together to create a best practices approach for Closed-Loop Change Control. CimTrak's value add is augmenting BMC's Change Management and Security processes with the ability to validate and verify that only expected and authorized changes are happening inside and outside the change management windows.
Operationally, only planned and authorized changes are allowed, exposing circumvented activity. The security impact is that all malicious changes are immediately exposed (zero-day) for removal and remediation.
The combined results deliver the necessary visibility and integrity assurance to deliver higher operational availability while mitigating the risk of security threats and breaches.
CimTrak's Integration with Helix ITSM Enables Customers to...
Create and Enforce a closed-loop environment for change management
Highlight Zero-Day malicious activity
Roll back and Remediate to a secure, trusted state
Identify unknown, unwanted, and unauthorized changes in real-time
Benefits of
CimTrak and BMC
CimTrak and BMC
Continuously detecting deviations from a “correct state” provides unprecedented value for both Security and IT Operations.
Identify and Detect Security Breaches
If you control change, you control security.
Next-Gen File Integrity Monitoring
Control and validate the integrity of OS and applications by detecting current file state against a known and trusted baseline or benchmark(s).
Trusted and Certified Benchmarks
CimTrak provides detailed alerts, reports, and controls for both CIS (Center for Internet Security) and DISA STIGs.
"Change Noise" Suppression
Only alert on unwanted, unauthorized, and unexpected activity.
Change Prevention
Prevent changes entirely for those files and directories that should never change.
Roll-Back and Remediation
Mean-Time-to-Restore (MTTR) to a correct and operational state is measured in seconds.
Compliance
Continuous and corrective guidance to ensure and attest that systems/devices remain in a state of compliance regardless of the regulatory mandate.
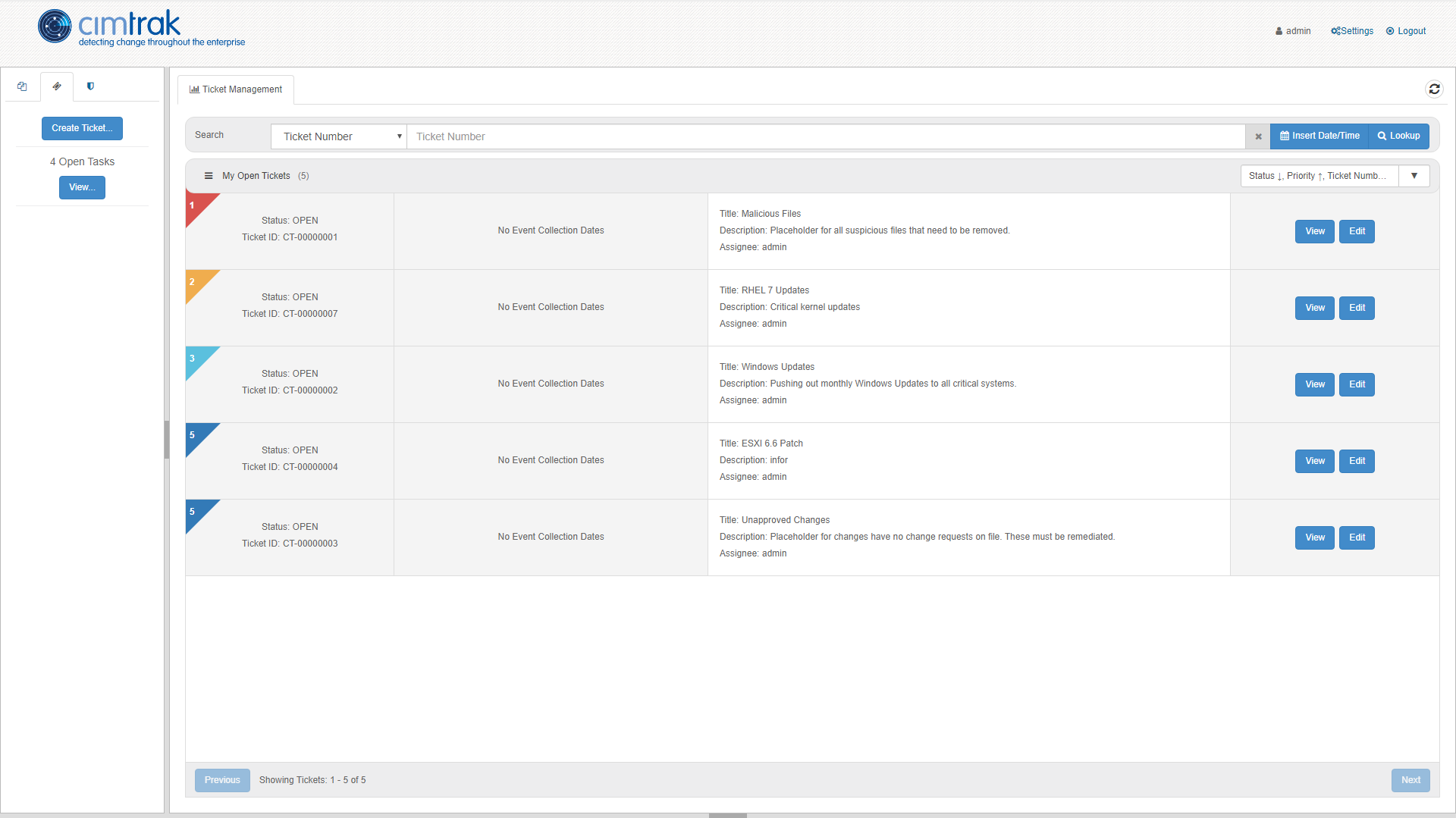
Compliance Workflow
Integrated ticketing system to manage compliance drift and remediation steps upon failed compliance tests.
Vulnerability Threat Management
Analyze and evaluate real-time security decisions and vulnerability posture with STIX/TAXII Feeds.
Tech Specs
The CimTrak Integrity Suite offers bi-directional ticket/incident synchronization through the use of an intermediary service (The CimTrak Ticket Syncer) that communicates between CimTrak and BMC Helix ITSM with the AR System REST API. Through the use of CimTrak with the Ticket Syncer, tickets/incidents created, modified, resolved or closed in either environment are synchronized in both environments.
Synchronization
Synchronization is achieved by polling both CimTrak and ITSM for changes in tickets since the last time polling occurred and creating/updating tickets of the out-of-date system. Configuration Items can be attached to the external ticket, the configuration item label/name (plus an optional prefix and suffix) will be matched to the agent name for a task in a CimTrak ticket.
See How
Closed-Loop Change Control
Closed-Loop Change Control
Mitigate security threats and breaches with the CimTrak and BMC integration.