CimTrak for Sophos
What We Monitor
Sophos UTM devices are firewall/VPN devices that provide controlled connectivity between an internal network and an external network (internet) while providing protection for the internal network by blocking traffic that isn’t explicitly allowed.
The VPN functionality allows encrypted external connections to the internal network by pre-configured authenticated users. Sophos UTM devices can be configured to provide additional security functions as well. CimTrak for Network Devices monitors the device configuration for changes, logs the changes, and then notifies the responsible parties.


How CimTrak for Sophos Works
When CimTrak locks a Sophos UTM device for monitoring, it reads the configuration of the device. It calculates a digital signature for the configuration, and store it in CimTrak’s master repository along with a copy of the configuration. At user-configured intervals, CimTrak reads the contents of the configuration, calculates the digital signature, and compares it to the signature stored in CimTrak’s master repository.
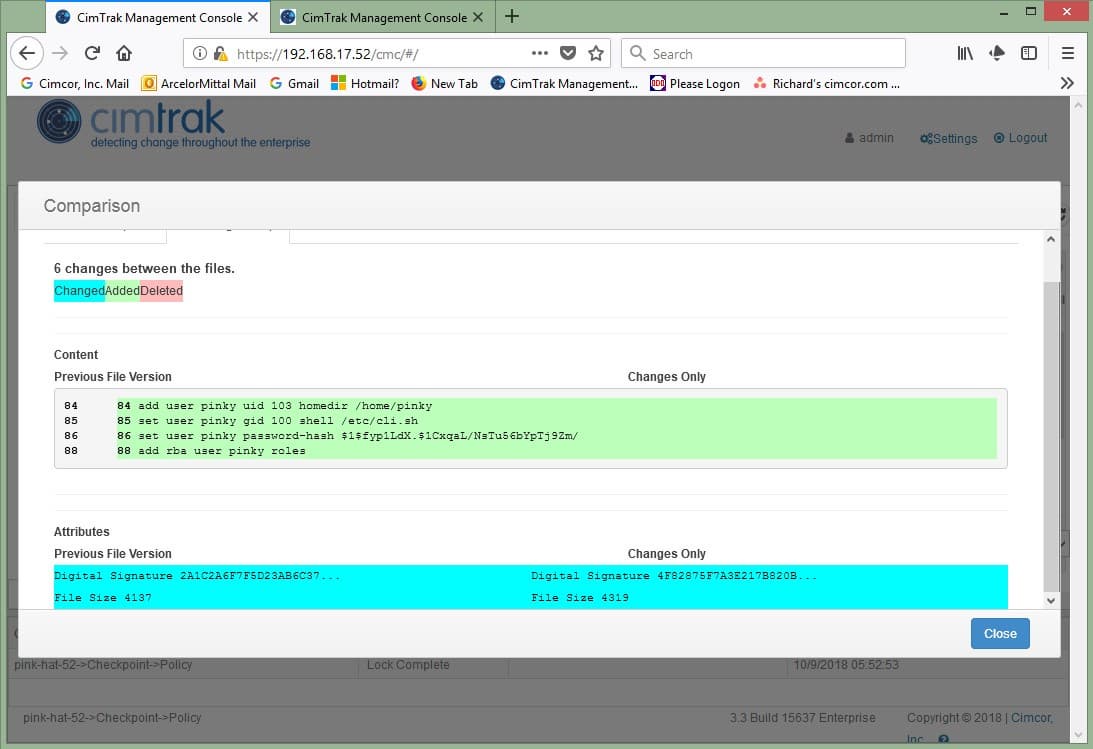
When CimTrak detects a change in the configuration, that configuration and its digital signature
CimTrak Product PDF
Get the CimTrak Technical Summary
Get a copy of our CimTrak Technical Summary, our in-depth guide to all its capabilities.
Try CimTrak for Free
Get your Free 30-day trial of CimTrak
Just let us know what capabilities you want to test out, and we'll set up a trial in your environment.
