Over the years, the DoD has undergone a series of bold cybersecurity initiatives, from embracing responsible vulnerability disclosure to the trailblazing Hack the Pentagon initiative. As cyber threats become more sophisticated, the DoD aimed to strengthen cybersecurity amongst its defense industrial base (DIBs) contractors by developing the Cybersecurity Maturity Model Certification (CMMC). In this article, we'll cover the top 10 things your organization needs to know about CMMC.
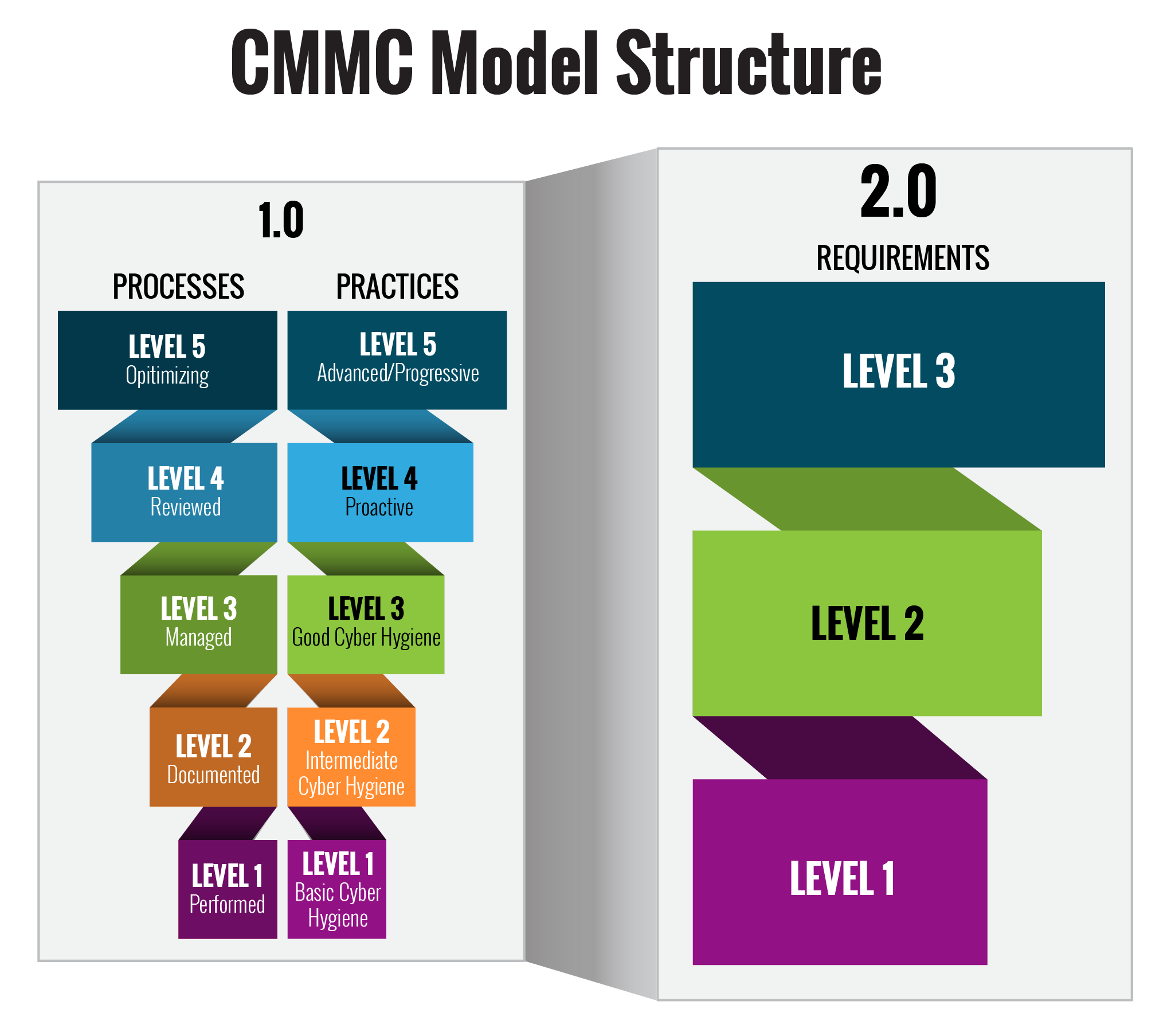
1. Compliance with CMMC 1.0 vs 2.0
With the publishing of CMMC 2.0, the interim Defense Federal Acquisition Regulation Supplement (DFARS) rule has established a five-year phase-in period, during which CMMC compliance is only required in select pilot contracts, as approved by the Office of the Under Secretary of Defense for Acquisition and Sustainment (OUSD(A&S)).
CMMC 2.0 will not be a contractual requirement until the Department of Defense completes the rulemaking process to implement the program.
2. CMMC 2.0 To Simplify Compliance for DIBs
The CMMC has relaunched its cybersecurity standards. With 100+ controls spread across 17 categories, CMMC is trying to ensure DIBs meet their particular level's compliance requirements while not making it too complex and cost-prohibited.
Level 1 mandates organizations to strictly adhere to fundamental cybersecurity protocols aimed at safeguarding Federal Contract Information (FCI), as outlined in FAR Clause 52.204-21. Currently, self-assessments will suffice to meet CMMC Level 1 requirements.
CMMC 2.0 Level 2 is equivalent to 800-171 and necessitates organizations to fortify their cybersecurity measures with enhanced practices, including stringent access control, proficient incident response strategies, and thorough media protection protocols.
The "Expert" level (Level 3), presently in development, will incorporate elements from both NIST 800-171 and a specific subset of NIST SP 800-172 requirements.
3. CMMC Is Based on NIST Frameworks
Unsurprisingly, the controls set out by NIST 800-171 form the bedrock of CMMC. NIST 800-171 was developed in response to FISMA in 2002 and positioned as a ‘competitive advantage’ (but not a requirement) for most DoD contracts.
With the release of CMMC 2.0, contractors and subcontractors need to brush up on their NIST standards as CMMC shifts to align closer to NIST 800-171 as well as NIST 800-172 requirements. As a result, one major change to the framework is moving away from the original 5-tiered approach to a 3-tiered approach, eliminating levels two and four.
4. CMMC is Essential for ALL DoD Contractors and Subcontractors
CMMC is essential for all DoD contractors and subcontractors. The level of compliance needed will vary depending on the nature of each contract.
Level 3 contractors certified under CMMC 2.0 must guarantee that their subcontractors adhere to the necessary cybersecurity standards at the designated level. This obligation is often specified in the contractual agreements between the main contractor and subcontractors. The vigilance in enforcing CMMC regulations across the supply chain is paramount for upholding the security stance of the entire network. Consequently, Level 3 contractors must proactively supervise subcontractors to verify adherence to the cybersecurity criteria.
5. CUI and FCI is the Focus
FCI, or Federal Contract Information, pertains to the unclassified data supplied by or formulated for the government within the confines of a federal contract. FCI specifically excludes information designated for public dissemination. On the other hand, CUI, or Controlled Unclassified Information, encompasses a broader spectrum of confidential data necessitating safeguarding as per diverse laws, regulations, or governmental directives. While FCI falls under CUI, the latter extends its coverage to encompass additional classes of sensitive information beyond those originating from federal contracts.
6. No Certification, No Bid, Not Yet
In early 2025, it is projected that companies vying for defense contracts will need to adhere to CMMC requirements. Unlike previous regulations, the current CMMC standards offer a more efficient framework to foster compliance and responsibility. Contractors and subcontractors impacted by these requirements should initiate their compliance preparations promptly, bolstering their defenses against continual targeting by sophisticated and persistent threat actors.
7. Three-Tier Certification and Assessment
Fortunately for many current and prospective DoD contractors, not all contractors will have to evidence the same CMMC certification level. The framework is divided into three levels with a focus on protecting CUI and FCI:
Level 1: Foundational - A set of 15 stipulations centered on safeguarding FCI aligning with fundamental protection outlined in 48 CFR 52.204-21 is required. If a DIB enterprise does not transmit, store, or process CUI on its unclassified network but handles FCI in these capacities, it can conduct a self-assessment at CMMC Level 1.
Level 2: Advanced - There are 110 requirements, encompassing both NIST SP 800-171 and DFARS 252.204-7012 standards. Evaluation procedures vary depending on contract specifications, involving triannual third-party assessments or annual self-assessments for specific programs. Contractors handling the transmission, storage, or processing of CUI must uphold compliance with CMMC Level 2.
Level 3: Expert - A total of 110 requirements from CMMC Level 2 will be augmented by an extra 24 requirements from NIST SP 800-172. Specialized contractors with specific mandates will necessitate compliance with CMMC Level 3, entailing external assessments by government/certified personnel every three years.
8. Assessment Include Physical Inspections
Unlike other prominent cybersecurity compliance frameworks, some CMMC assessments will be carried out in person by a C3PAO. (Primarily assessments for Level 2 and 3 certifications.)
Contractors aiming to become certified must generate and maintain evidence that their systems and processes align with CMMC requirements. Simply being compliant isn’t enough — you must be able to prove it.
9. CMMC 2.0 Phased Implementation
Given the framework’s comprehensive nature, CMMC has been a gradual implementation process, but the release of version 2.0 hasn't postponed the initial timeline.
The currently published timeline looks like this:
.jpg?width=730&height=439&name=CMMC%20Timeline%20(2).jpg)
10. Gap Analysis Doesn't Have to be Manual
Identifying compliance gaps is one of the most challenging aspects of complying with any cybersecurity framework. Traditionally, organizations have relied on a combination of internal and external audits to ensure they have the controls and evidence necessary to pass an official assessment.
However, even the best assessments are only a point-in-time judgment of compliance. For technical controls, it’s easy for routine changes and updates to cause previously compliant systems to fall out of compliance. If this happens between assessments, it could be weeks or months before the issue is identified and fixed.
Fortunately, your gap analysis process doesn’t have to be a part of the manual grind.
CimTrak is an IT integrity, security, and compliance tool that makes it easy for organizations to identify and resolve CMMC non-compliance issues in IT systems and assets. In a single scan, CimTrak can highlight any configuration or security issues that don’t comply with CMMC.
Taking things to the next level, CimTrak continuously monitors your environment and detects changes to assets, files, and accounts. When a change occurs that pulls an asset or system out of CMMC compliance, CimTrak raises an alert and a report, making it easy to resolve the issue quickly.
Crucially, CimTrak’s functionality maps directly to many of the control objectives of CMMC.
- AC - Access Control
- AM - Asset Management
- AU - Audit and Accountability
- CM - Configuration Management
- IR - Incident Response
- RE - Recovery
- RM - Risk Management
- SA - Security Assessment
- SC - System & Communication Protection
- SI - System & Information Integrity
To learn more about how CimTrak can help your organization align its security strategy and processes with CMMC, download the CMMC Solution Brief today.
Tags:
Compliance
March 21, 2024